- All Cases
- Penetration Testing Enterprise
SiriusOne:
Penetration Testing for Enterprise Systems
Manual-first penetration testing — simulating real attacker behavior across web, API, mobile, and cloud layers.Client & Project Overview
Business Problem
"We don’t just test systems — we challenge assumptions. Our goal was to turn scanning into validation and reports into decisions."
Eugene Fateev
Lead Cybersecurity Engineer, SiriusOne
Tech Stack
Cloud: AWS (IAM, WAF)
Apps: Web, APIs, iOS, Android
CI/CD: GitLab
Security: Burp Suite, OWASP ZAP, Nmap, Metasploit, Intruder, Gitleaks, Docker Scout, Dependency-Track
Frameworks: OWASP Top 10, NIST 800-115, OSSTMM, ASVS
#Cybersecurity
#Penetration Testing
#DevSecOps
Project Timeline

Duration
3 weeks
Effort
240 hours
Discovery & Research
Days 1–3
External footprinting, asset inventory, tech-stack mapping, scoping and rules of engagement confirmed.
Design & Prototyping
Days 4–8
Threat modeling, test design, abuse-case mapping, data-flow validation, safe-test constraints and success criteria.
Development
Days 9–15
Manual exploitation of prioritized vectors, auth and access control validation, API chaining, mobile app review, and WAF probe tests.
Testing & Security Audit
Days 16–18
Risk validation, impact confirmation, SBOM/dependency checks, CI/CD secrets audit, cloud/IAM spot checks, and evidence collection.
Deployment & Training
Days 19–21
Executive report, risk matrix and remediation plan; stakeholder workshop, developer hand-off, and retest window scheduling.
Team involved
Cybersecurity Architect
OWASP/NIST alignment, threat modeling, risk policy.
Red Team Lead
Manual exploitation, lateral movement, bypass tactics.
DevSecOps Engineer
CI/CD, secrets management, pipeline hardening.
Cloud Architect
AWS IAM/WAF review, perimeter and posture checks.
Project Manager
Governance, cadence, delivery and stakeholder alignment.
Solution Overview
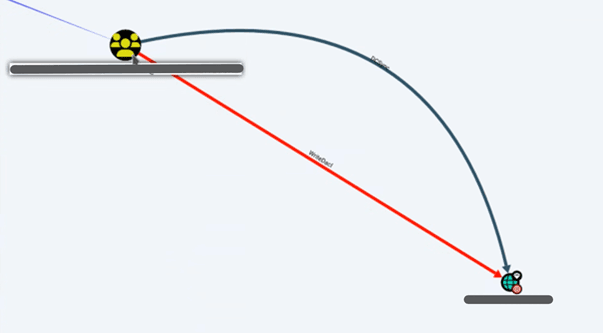
Web & API Testing
Injection, authz/authn, access control and data-exposure validation with chained-attack scenarios.
Mobile App Testing
Transport security, storage risks, code/obfuscation review, API linkage and device-level misconfig checks.
Cloud & IAM Review
Privilege paths, public exposure, WAF rules, logging, and least-privilege hygiene.
CI/CD & Secrets Audit
Token leakage, runner permissions, artifact trust, dependency risk and SBOM verification.
WAF & Edge Validation
OWASP Top 10 probes, false-negative checks and rule-tuning guidance with reproducible evidence.
Results
60% Reduction in Exposure Window
Faster discovery-to-fix through prioritized remediation and playbooks.
Critical Findings Uncovered
Business-logic chains and 5 critical issues missed by prior automated scans were validated and fixed.
Hardened CI/CD & Dependencies
Secrets protection, runner isolation, SBOM and dependency governance improved.
Compliance & Confidence
ASVS/OWASP coverage demonstrated; clearer audit trail for internal and external stakeholders.

Similar
implemented cases: